Browse Our Knowledge Base
Identifying and Reporting Email Scams
Overview
It’s important to stay alert when interacting with unexpected emails. Most people receive spam messages regularly and many of them are automatically filtered into Junk or Other folders. The emails that require the most caution, however, are phishing attempts.
Phishing is a type of deceptive attack designed to trick you into sharing sensitive information (such as your login credentials or payment details) or to install malware on your device. The ultimate goal is often to take control of your account and use it to target others. Knowing how to recognize phishing emails is the best way to protect yourself and the cmapus community.
Identifying phishing emails
If you receive an email that seems suspicious, use the tips below to determine whether it’s legitimate or a scam.
1. Check the sender.
The display name and the actual email address may not match. For example, an email that appears to be from the “Chancellor” but comes from a Gmail address is almost certainly a scam.
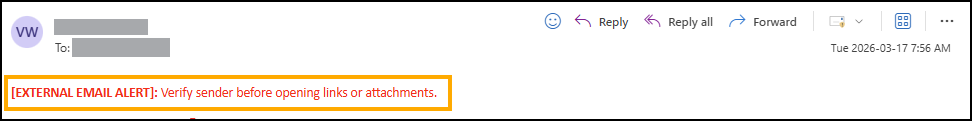
Note: All emails sent from non‑SIU accounts will include the banner:
[EXTERNAL EMAIL ALERT]: Verify sender before opening links or attachments.
This does not automatically mean the email is malicious, but it should prompt you to take a closer look at the sender.
2. Verify links and attachments.
Phishing emails often include links or attachments (such as PDFs or Word documents).
- On a computer, hover your mouse over a link to preview where it would take you if clicked.
- If an email claims to be from SalukiTech or another SIU department but the link does not lead to an siu.edu website, it is likely a scam.
- Emails that contain only an attachment with no explanation or context should be treated as suspicious.
3. Look for improper spelling/grammar.
Many scam emails contain noticeable spelling or grammar mistakes, odd spacing, random capitalization, or awkward phrasing. These can indicate that the message was generated or translated automatically. Official SIU communications are reviewed for accuracy and professionalism.
4. Be wary of messages using urgent/threatening language.
Emails that pressure you to act immediately (such as warnings that your account will be deleted or suspended) are common phishing tactics. Legitimate SIU notices about password expirations or account changes provide advance notice (typically at least 30 days) and come from NoReply@siu.edu.
5. Be cautious of job offers or money-related messages.
Unsolicited emails offering high pay for vague or undefined work are often scams. These messages typically lack clear job descriptions and may reference the need for an “assistant” without details.
Important: If a job offer email asks you to print or deposit a check, stop communicating immediately. If you have shared any banking information, contact your bank as soon as possible.
Note: If you’re ever unsure whether an email is legitimate, contact SalukiTech. We’re happy to help you determine whether a message is real or a phishing attempt.
Reporting phishing emails
Reporting phishing can now be done in Outlook. Here are brief instructions:
- Website:
- Method 1: Right click on the email and look for Report > Report Phishing.
- Method 2: Click the three horizontal dots in the upper right corner of the email above the timestamp and look for Report > Report Phishing.
- Desktop Client:
- Method 1: Click on the “Report Message” button in the upper right corner of the window. Select Phishing.
- Method 2: Right click on the email and look for Report > Report Phishing.
- Android app:
- Tap the three vertical dots underneath the timestamp in the email (NOT in the blue bar). Tap the image that looks like an envelope on a fish hook.
Junk emails
Junk mail is different from phishing emails, and it does not have to be reported to the university. Junk can be business advertisements, newsletters, or anything that doesn’t seem malicious.
From the Outlook website or desktop client, you can mark it as junk by right clicking the email from your inbox and selecting ‘mark as junk’.